|
This is a collection of sites about security. |
Document
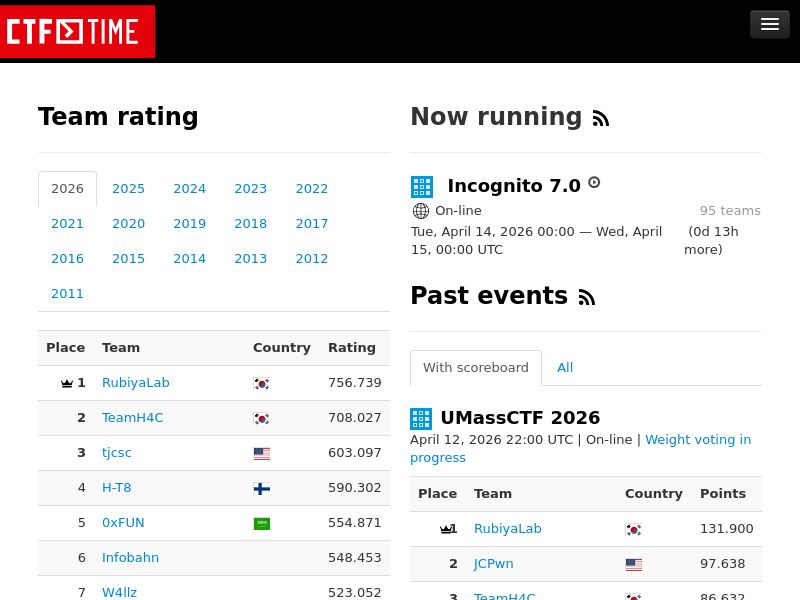
Education,Training
Cloud Security Posture Management
AI